Cyber Extortion or Blackmail
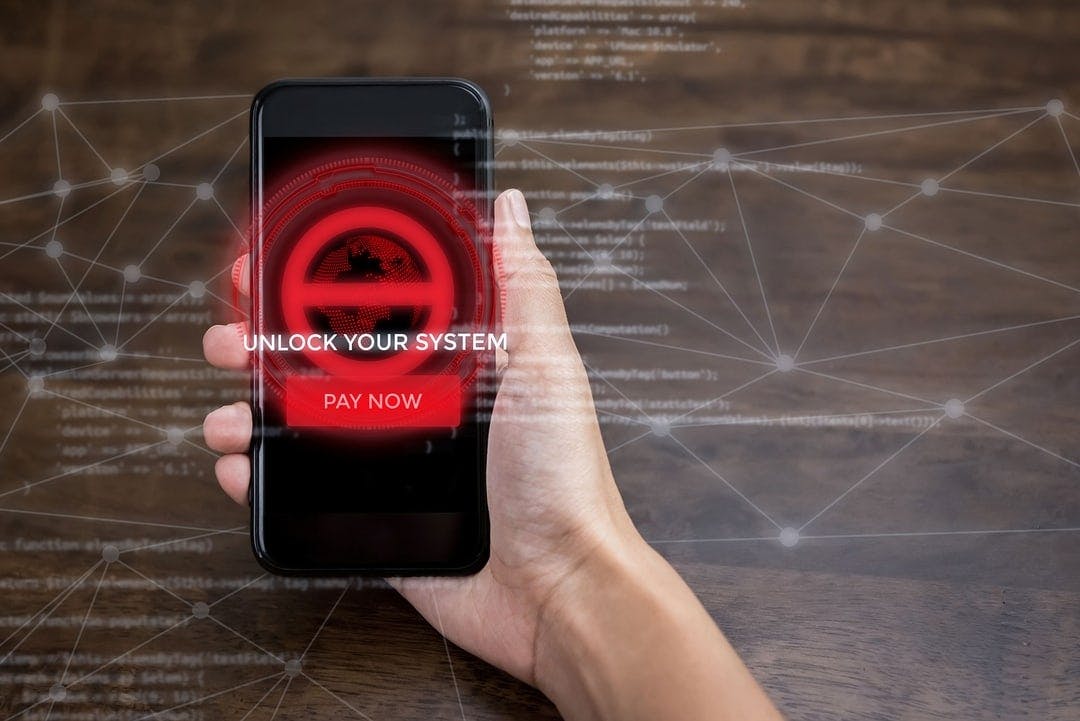
Cyber extortion or blackmail
IDCARE has observed an 80% increase in cyber extortion/blackmail cases between June and July 2018 and we are only half way through the month! Scammers are now emailing potential targets, quoting a password that you have used in the past. The email says they have incriminating video footage that will be shared with family and friends. The scammers demand payment (often Bitcoin) and threaten negative consequences to the victim if the victim doesn't comply with the demands.
How it works
The extortion scammer sends an email that says they have captured video footage of the recipient showing the person involved in explicit behaviour. They say this was accessed via malicious malware previously downloaded onto their computer. The extortion scammers often threaten that if the recipient of the email does not pay the ‘one off’ demand for money within 24-48 hours they will expose the explicit material to all of their contacts (supposedly also downloaded during the attack).
In our experience most of these blackmail threats to expose information/hack accounts or compromising photos/videos are nothing more than a bluff. IDCARE has been contacted by many clients over the past 4 years who have also been victim to blackmail just like this. So far no one has reported that the scammer followed through with their threats. While no extortion attempt can be completely discounted, the likelihood of the criminal going ahead with these threats is minimal.
It is important to remember that the motivation of the scammer is financial gain. They are not going to gain anything by following through with their threat to expose illicit material. They make their money through intimidation and fear of exposure. Furthermore, if you do choose to pay them they are likely to keep coming back with further demands for money as they see you as a soft target. Scammers will keep trying until they recognise that they have exhausted the ability for the victim to pay. That's why it's important that you cut all ties by blocking all avenues THROUGH which these criminals can contact you.
Ways you can avoid getting caught up in extortion scams
- Cover your webcam on all devices when not in use
- Change your passwords regularly
- Make all passwords unique to the online service you are applying them to
- Run anti-virus software regularly and install software updates when available
Most commonly reported extortion scams:
Webcam hack: This is where the scammer tells the target they have had access to the user’s webcam for a period of time and have managed to capture compromising video of them. These threats will be general, eg. the user was captured doing everyday things in their homes half-dressed, and/or sometimes specific eg. if the user has recently visited a pornography website or other unsecure website and they receive an email soon after.
Illicit acts: Scammers will pose as someone looking for an online relationship. Once trust has been establish (often within hours of connecting) scammers will request the victim to record an illicit act to send to them. Scammers will then use the video to blackmail the individual.
Compromised/hacking accounts: Scammers will obtain small amounts of personal information such as user names or passwords associated to a websites that have been breached, then email the information to the user to convince them their systems have been compromised.
Assignment extortion: Scammers will set up websites offering to do university assignments for a fee. Once paid, the student will instead receive a threatening email telling them the website owners will expose them to the university unless they pay an additional fee.
How do scammers get this information?
Passwords and users names are often collected by scammers through the use of malicious software unintentionally downloaded by the Internet user through a phishing email or visiting an unsecure website. It can also happen when a phishing email redirects the receiver to a website that mirrors a legitimate site, prompting the user to ‘log in’ resulting in the capture of information.
As data breaches are extremely common there is a good chance the information in the new extortion emails was first collected from the data set of a known breach. Data from data breaches is bought and sold to and from different scammers across the globe. Each scammer/group will have different agendas for what the data will be used for once obtained. For example some scammers may only be interested in accessing your account to pretend to be you in an attempt to scam your contacts. Other scammer’s may be interested in taking the log in information, sending you an email with the information and claiming to also have access to other online accounts.
As I write this, one of my personal email accounts has been involved in 3 separate KNOWN data breaches since 2015, one of which captured my email account password. My information may also have been exposed in other breaches that have never been recorded, unfortunately this is the nature of the ecosystem. As I change my passwords regularly there is less likelihood that my email may have been accessed.
You can check your email account to ensure it has not been compromised in a known breach by going to www.haveibeenpwned.com If your email is found to be associated with any listed known breaches, change your password immediately.
Disclaimer: Ransomware has been excluded from this article due to the difference in the nature of the cyber-attack. This scam information is also related to scams that are being perpetrated by scammers with no personal connection to the victim.
Join the global list of organisations making a real difference in people’s lives by supporting our service.














































Copyright © 2025, IDCARE. All Rights Reserved.
ABN 84 164 038 966








